Decommissioning legacy servers is like defusing bombs—one wrong move and you could have a disaster on your hands.
After successfully migrating our revenue cycle management applications to AWS, my team faced the equally challenging task of properly decommissioning eight on-premises locations across the US, Philippines, and India. This wasn’t simply a matter of unplugging servers and recycling hardware—it required meticulous planning to ensure data security and compliance with HIPAA regulations.
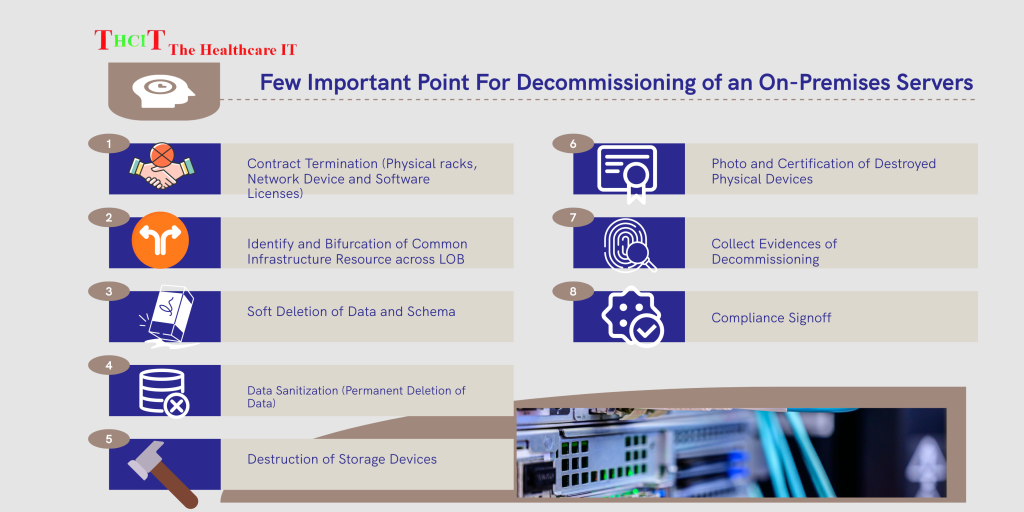
The process taught us valuable lessons about secure decommissioning in healthcare environments. First and foremost: data sanitization is non-negotiable. Every storage device needed to be properly wiped using methods that met HIPAA standards, with documentation to prove it had been done correctly.
Physical asset disposition presented another challenge. We needed to account for every piece of equipment, ensuring it was either securely destroyed or wiped and repurposed according to our security policies. This required coordination across multiple geographies and careful chain-of-custody documentation.
Perhaps the most critical aspect was verifying that no data remained accessible. This meant checking backups, replication sites, development environments, and even test systems to ensure patient information was completely removed or properly protected.
The process also highlighted the importance of stakeholder communication. Operations teams, security officers, compliance managers, and IT staff all needed clear information about the timeline and their responsibilities. Keeping 1,500 users informed during the transition required a comprehensive communication plan.
Have you been through a major decommissioning project? What challenges did you face in ensuring security and compliance? Share your experiences in the comments!
#DataSecurity #HIPAA #CloudMigration


